
Understanding Technical Debt in Cloud Architecture: Definition and Impact
This article offers a comprehensive overview of technical debt within cloud architecture, a critical concept for organizations utilizing cloud service...
Discover the latest insights, tutorials and expert analysis on cloud computing, serverless architecture and modern technology solutions.
Stay updated with the latest trends and insights in cloud computing technology

This article offers a comprehensive overview of technical debt within cloud architecture, a critical concept for organizations utilizing cloud service...
This article provides a comprehensive comparison of Continuous Delivery and Continuous Deployment, two crucial methodologies for modern software devel...

Cloud-based businesses are increasingly vulnerable to Distributed Denial of Service (DDoS) attacks, which can disrupt online services and lead to subs...
This article delves into the world of serverless databases, exploring their core concepts, evolution, and advantages over traditional systems. You'll...

Digital Rights Management (DRM) is a critical component of the digital landscape, serving to protect intellectual property in the realm of content cre...
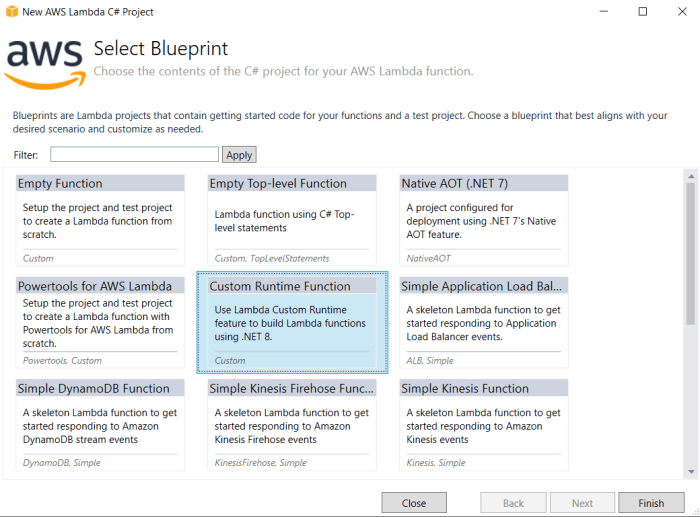
Unlock the full potential of AWS Lambda with custom runtimes. This comprehensive guide delves into the definition, benefits, and implementation of cus...
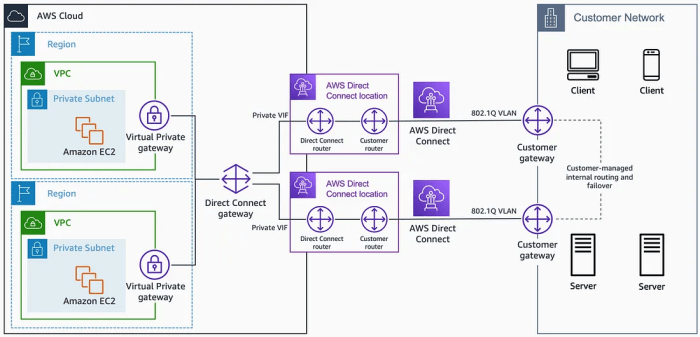
This comprehensive guide explores Direct Connect and ExpressRoute, essential services for establishing secure and reliable hybrid cloud connectivity....
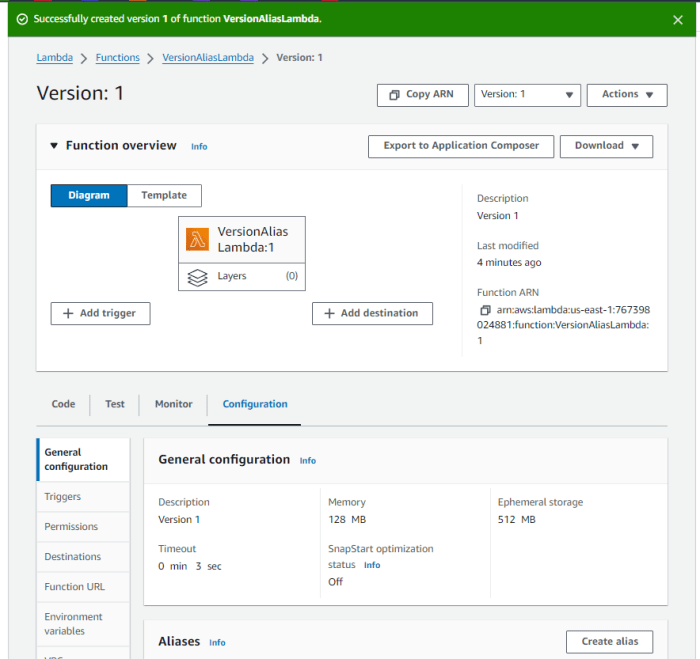
This comprehensive guide delves into the critical concepts of Lambda function versions and aliases, explaining their distinct roles in managing and de...

Serverless API gateway proxy integration is a fundamental concept in modern serverless architecture, acting as a critical link between client applicat...
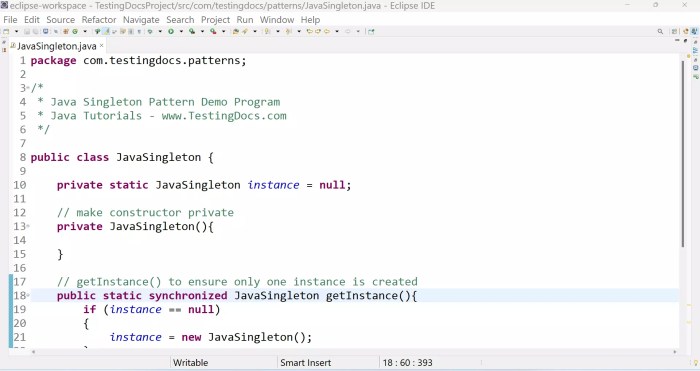
The Singleton pattern provides a method for controlling object instantiation, ensuring only one instance of a class exists with global access. While t...

The KISS (Keep It Simple, Stupid) principle is a powerful concept advocating for clarity and efficiency by prioritizing ease of understanding and exec...

Privacy-preserving computation offers a groundbreaking approach to data security, enabling the processing of encrypted data without the need for decry...