Implementing Least Privilege Access in the Cloud: A Practical Guide
Securing cloud resources is critical, and implementing Least Privilege Access (LPA) is a foundational security practice. LPA limits user and applicati...
152 posts in this category
Securing cloud resources is critical, and implementing Least Privilege Access (LPA) is a foundational security practice. LPA limits user and applicati...

Navigate the complex legal landscape of cloud computing with this comprehensive guide. This article delves into critical areas like data privacy regul...

Organizations face increasing cyber threats, making robust security awareness training for employees crucial. This comprehensive guide provides a step...
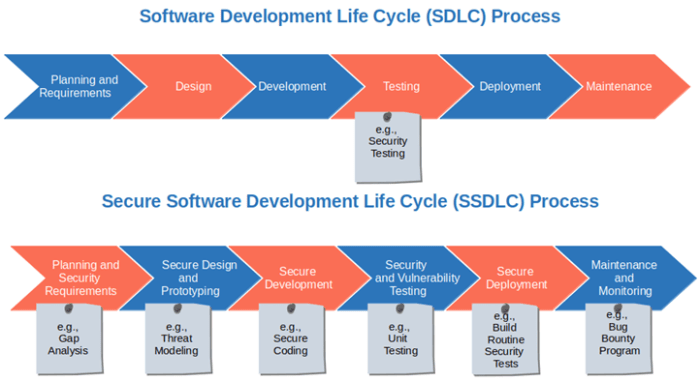
Protecting your software from vulnerabilities is paramount in today's digital world, and this guide provides a comprehensive approach to implementing...
This comprehensive guide details the essential skills required to excel as a Cloud Security Engineer, covering core technical competencies like networ...
This comprehensive guide provides a detailed roadmap for implementing Single Sign-On (SSO) across your enterprise applications. From understanding the...

This comprehensive guide delves into the critical role of Cloud Workload Protection Platforms (CWPP) in modern cloud security, exploring its core conc...
Managing security across a multi-cloud environment requires a strategic approach to avoid fragmentation and ensure consistent protection. This guide o...
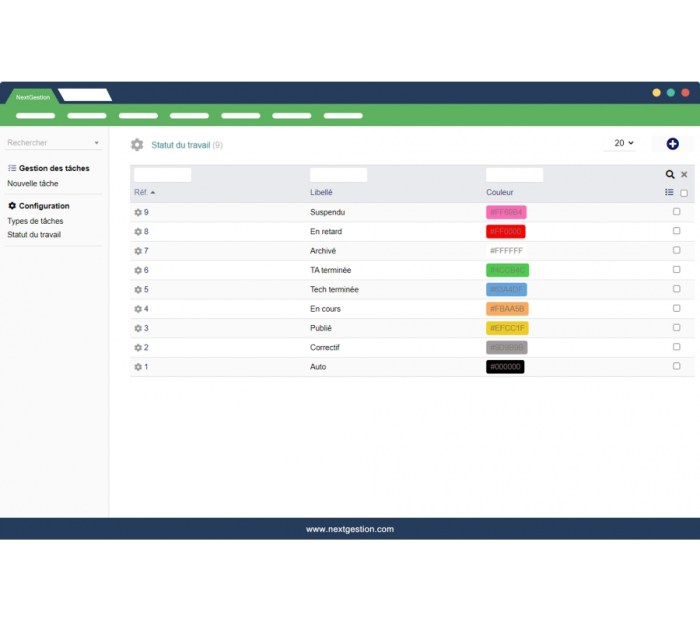
User Lifecycle Management (ULM) and provisioning are crucial for security, operational efficiency, and compliance within any organization. This guide...
Safeguarding your digital assets requires vigilant monitoring for unauthorized file changes. This article explores the critical importance of detectin...
Prepare for the future of cybersecurity with a comprehensive guide to Post-Quantum Cryptography (PQC). This article delves into the fundamental concep...

This article provides a comprehensive overview of Data Privacy Impact Assessments (DPIAs), essential tools for protecting personal information in the...