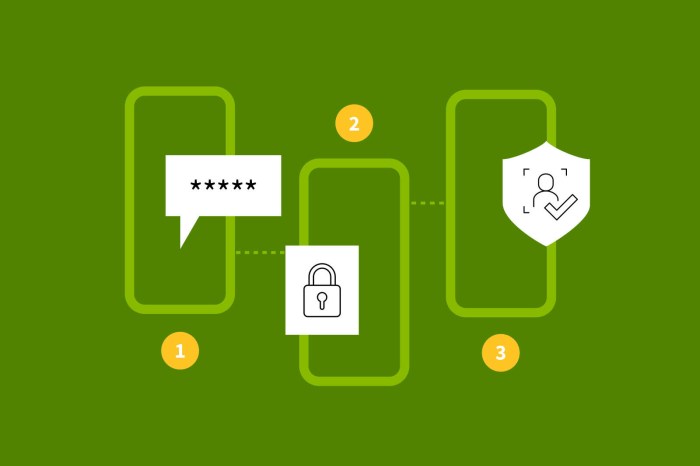
Enforcing Strong Authentication & Multi-Factor Authentication: A Comprehensive Guide
Protecting sensitive data in the digital age demands robust security measures. This guide provides a detailed overview of enforcing strong authenticat...
152 posts in this category
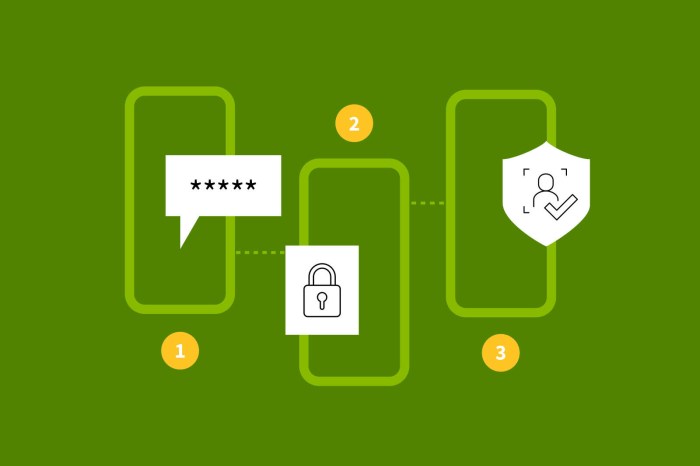
Protecting sensitive data in the digital age demands robust security measures. This guide provides a detailed overview of enforcing strong authenticat...

This article provides a comprehensive overview of User and Entity Behavior Analytics (UEBA), exploring its core concepts, components, and practical ap...

This article provides a comprehensive overview of runtime security for containers, emphasizing its critical role in protecting containerized applicati...

Data classification is a fundamental practice in information security, involving the categorization of data based on its sensitivity and importance. T...
This article provides a comprehensive guide to implementing a Zero Trust security model within cloud environments, covering key principles, asset iden...
In today's complex regulatory environment, establishing a robust data retention policy is crucial for compliance and minimizing potential risks. This...
In the world of interconnected microservices, secure service-to-service communication is critical. Mutual Transport Layer Security (mTLS) provides a p...
This article delves into the critical practice of Continuous Compliance Monitoring (CCM) in cloud environments, explaining its core concepts and showc...

Navigating HIPAA compliance in the cloud requires a strategic approach that addresses data security, access controls, and disaster recovery. This comp...
Handling cardholder data in the cloud necessitates adherence to Payment Card Industry Data Security Standard (PCI DSS) compliance. This guide provides...

Navigating SOC 2 compliance in a cloud environment requires a strategic approach, and this article provides a comprehensive guide. It covers essential...
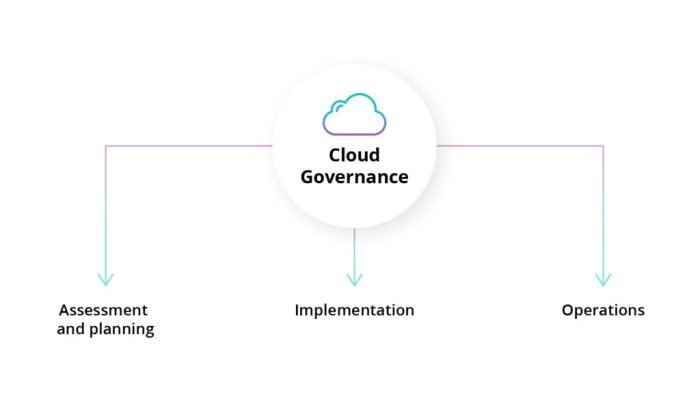
Establishing a formal cloud security governance framework is crucial for protecting valuable assets and maintaining compliance in the cloud. This fram...