
Tactics, Techniques, and Procedures (TTPs): A Comprehensive Guide
This article provides a comprehensive guide to Tactics, Techniques, and Procedures (TTPs), crucial elements for understanding and combating cyber thre...
152 posts in this category

This article provides a comprehensive guide to Tactics, Techniques, and Procedures (TTPs), crucial elements for understanding and combating cyber thre...

A security baseline serves as the foundation for robust cybersecurity, providing a standardized configuration for systems and applications to ensure a...

This comprehensive guide explores the ISO 27001 standard, a globally recognized framework for information security management. From its core principl...
Navigating a cloud security audit can seem daunting, but this comprehensive guide provides a clear roadmap for preparation and success. The article me...

This article provides a comprehensive overview of Software Bill of Materials (SBOMs), explaining their definition, purpose, and benefits for various s...
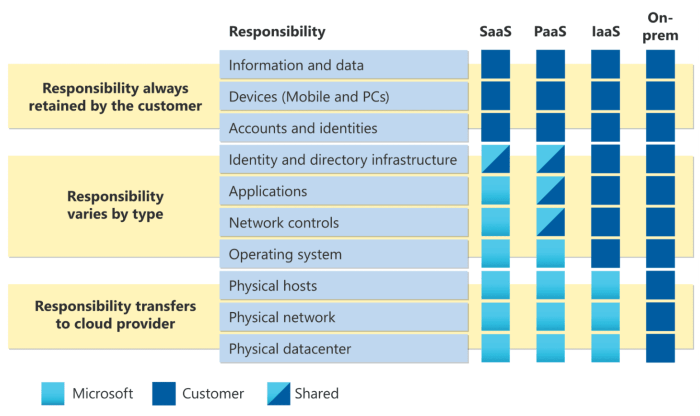
In an increasingly cloud-dependent business environment, establishing a strong cloud security team is crucial for protecting valuable data and applica...
This article explores the critical need to protect "data in use," delving into the inherent security risks and challenges associated with active compu...
This article provides a comprehensive guide to preventing Cross-Site Scripting (XSS) attacks, detailing the fundamental concepts, various attack types...

This article provides a comprehensive guide to preventing SQL injection attacks specifically within cloud application environments. It covers critical...
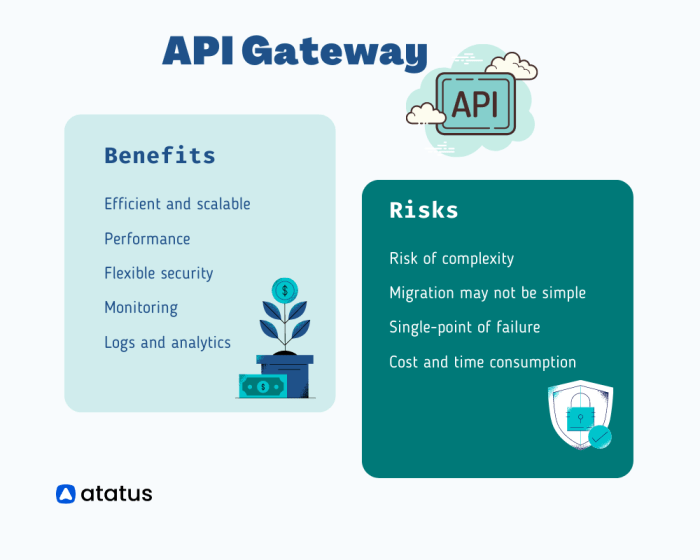
API gateways are vital components of modern application architectures, acting as the primary point of entry and security for all API traffic. Understa...
This comprehensive guide explores the multifaceted landscape of container security, outlining critical best practices to protect your deployments from...

In the modern cloud-centric business environment, robust data and infrastructure security is critical. Security Information and Event Management (SIEM...