
Integrating Threat Intelligence for Enhanced Cloud Security Operations
This article explores the vital integration of threat intelligence into cloud security operations, a crucial step in defending against modern cyber th...
152 posts in this category

This article explores the vital integration of threat intelligence into cloud security operations, a crucial step in defending against modern cyber th...

Protecting sensitive data within big data platforms demands a comprehensive approach encompassing encryption, access control, data governance, and rob...

Securing your critical digital assets starts with effective Privileged Access Management (PAM). This article provides a comprehensive, practical guide...

Handling Data Subject Access Requests (DSARs) is a critical component of GDPR compliance. This comprehensive guide offers a clear and detailed roadmap...
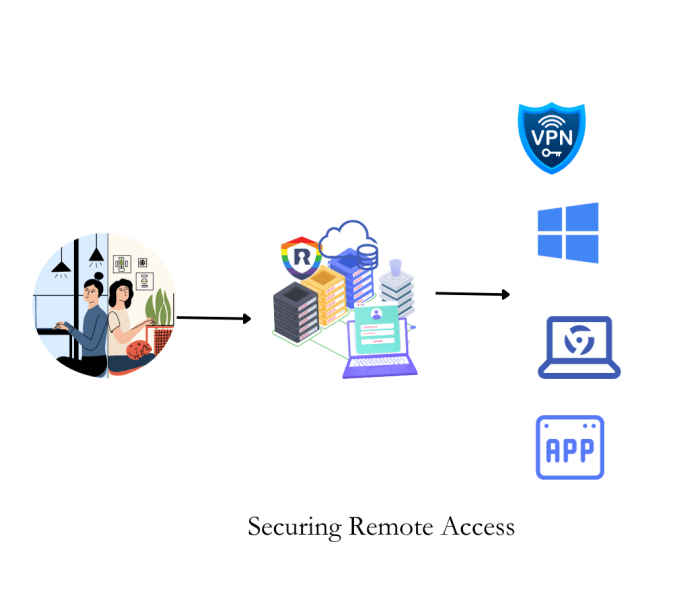
Securing remote access to cloud environments is paramount in today's interconnected landscape, yet presents significant security challenges. This guid...
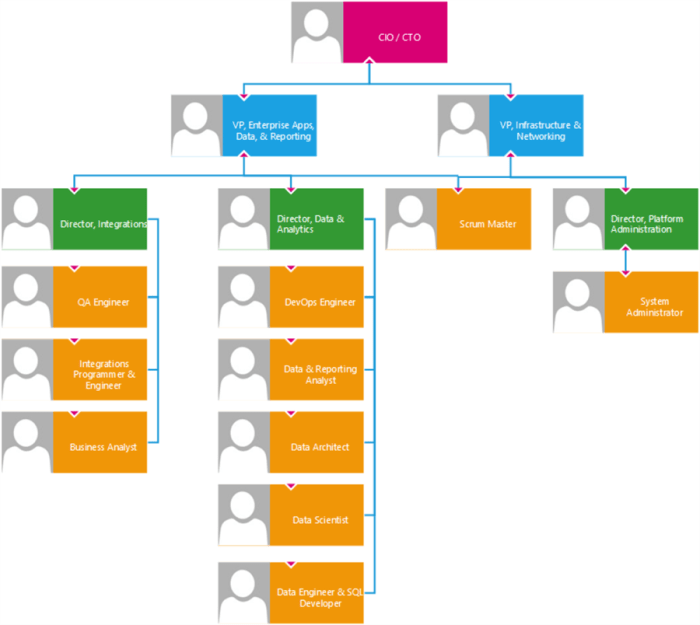
Cloud computing's scalability demands stringent security measures, making clear role and responsibility definitions for cloud access paramount. This a...
Discover insights and practical tips in this comprehensive guide about What Are The Compliance Requirements For Data Breach Notifications.

This article comprehensively explores the "Right to Be Forgotten," a critical aspect of data privacy laws, detailing its origins, legal frameworks, an...
Cybersecurity is a dynamic field, and bolstering your security posture requires a proactive, ongoing approach. This article outlines a strategic frame...

This article provides a comprehensive overview of the Common Vulnerabilities and Exposures (CVE) database, detailing its purpose, structure, and the r...

Cloud-based businesses are increasingly vulnerable to Distributed Denial of Service (DDoS) attacks, which can disrupt online services and lead to subs...
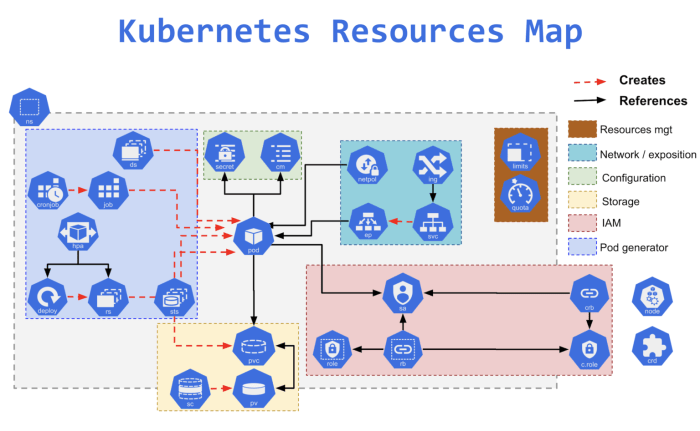
Kubernetes Pod Security Policies (PSPs) are crucial for bolstering the security of your containerized applications within a Kubernetes cluster. These...