
Key Risk Indicators (KRIs) for Cybersecurity: A Comprehensive Guide
Cybersecurity Key Risk Indicators (KRIs) serve as vital early warning signals, enabling organizations to proactively manage and mitigate evolving cybe...
152 posts in this category

Cybersecurity Key Risk Indicators (KRIs) serve as vital early warning signals, enabling organizations to proactively manage and mitigate evolving cybe...
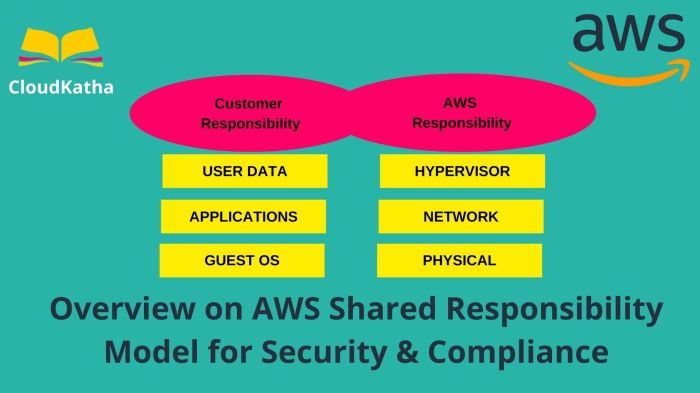
The shared responsibility model is a critical framework in cloud security, outlining the security obligations of both the cloud provider and the custo...

This guide provides a comprehensive roadmap for establishing robust threat hunting capabilities, essential for proactively identifying and mitigating...

Protecting your organization from internal cybersecurity risks is paramount. This guide, "How to Detect and Respond to Insider Threats," offers a comp...

This article provides a comprehensive overview of Static Application Security Testing (SAST), exploring its core principles, role within the Software...
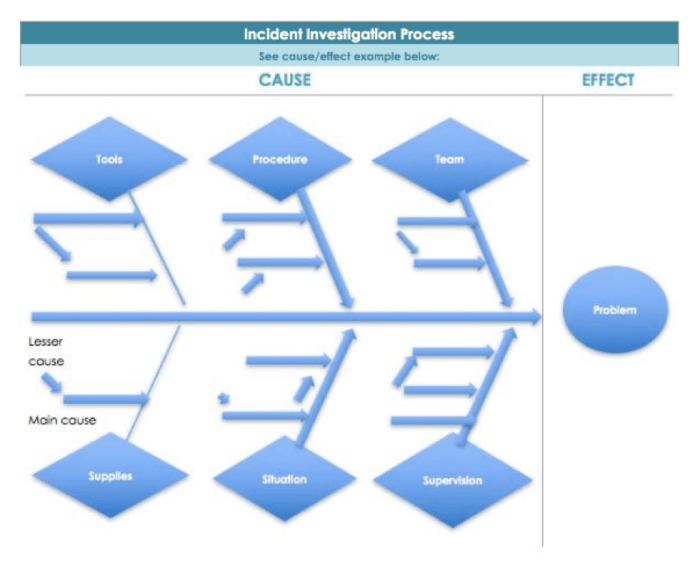
This article provides a comprehensive guide to performing a Root Cause Analysis (RCA) following a security incident, a crucial skill in today's digita...

In the face of ever-evolving digital threats, organizations need efficient and proactive security solutions. Automated security remediation offers a p...

In today's evolving digital landscape, cloud security certifications are crucial for professionals seeking to validate their expertise and advance the...

This comprehensive guide provides a detailed overview of securing the Kubernetes control plane, covering essential aspects from authentication and aut...
This comprehensive article explores the concept of honeypots in cybersecurity, detailing their purpose, diverse types (low, medium, and high-interacti...

Cloud governance is essential for successful cloud adoption, and "policy as code" is revolutionizing how organizations manage and secure their environ...

This article provides a comprehensive overview of security maturity models, essential frameworks for enhancing an organization's cybersecurity posture...