
Cloud Incident Response Plan: A Comprehensive Development Guide
Navigating the complexities of cloud security requires a proactive approach, beginning with a comprehensive incident response plan. This guide highlig...
152 posts in this category

Navigating the complexities of cloud security requires a proactive approach, beginning with a comprehensive incident response plan. This guide highlig...
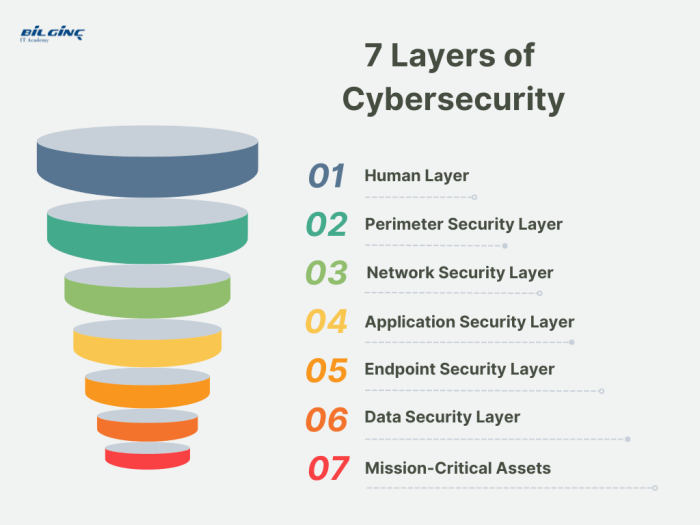
Defense in depth is a critical cybersecurity principle that emphasizes a layered approach to security, acknowledging that no single measure is impenet...

Cloud systems demand constant vigilance to ensure both security and optimal performance. This guide outlines essential strategies and best practices f...
This comprehensive guide explores the transformative power of Zero Trust Network Access (ZTNA) in modern cybersecurity, outlining its core principles...

In the face of ever-evolving cyber threats, tabletop exercises are vital for strengthening an organization's incident response capabilities. These dyn...

This article delves into the critical process of de-provisioning user accounts, explaining its definition, triggers, and the vital role it plays in bo...

This article delves into the OWASP Top 10, the definitive guide to web application security risks. It provides a comprehensive overview of the most c...

In the ever-evolving cloud environment, safeguarding your digital assets is critical, and Cloud Infrastructure Entitlement Management (CIEM) tools off...

In the ever-evolving digital world, File Integrity Monitoring (FIM) serves as a crucial security layer, vigilantly protecting your data and systems fr...
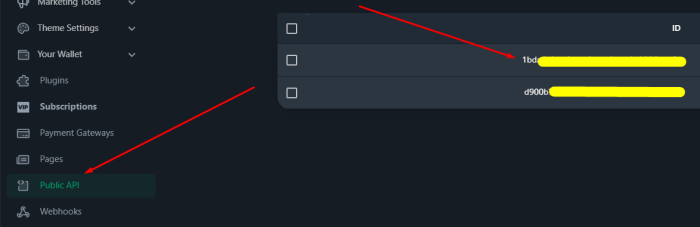
Protecting sensitive API keys and tokens is crucial for maintaining application security and preventing costly data breaches. This article provides a...

This article provides an introduction to threat modeling using the STRIDE methodology, a critical practice for enhancing software security. Learn how...
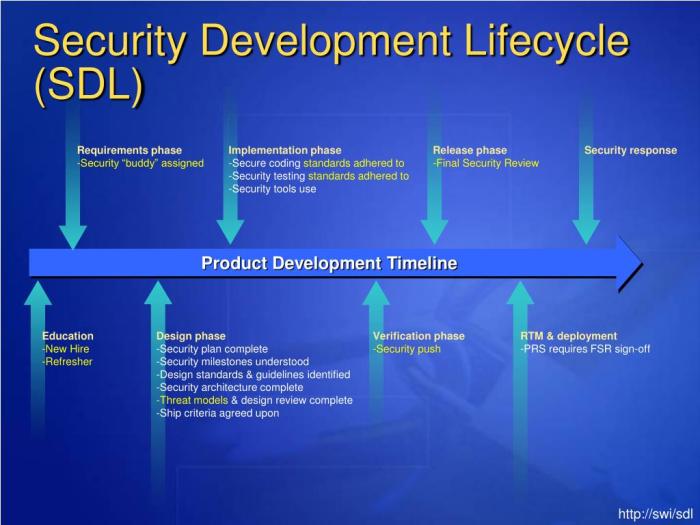
"Shifting security left" is a critical strategy for modern software development, emphasizing the integration of security practices early in the develo...