
Cloud-Based Master Data Management: A Comprehensive Guide
This comprehensive guide explores the evolving landscape of Master Data Management (MDM) in the cloud, examining its architecture, data integration st...
175 posts in this category

This comprehensive guide explores the evolving landscape of Master Data Management (MDM) in the cloud, examining its architecture, data integration st...

This article offers a practical roadmap for seamlessly integrating Artificial Intelligence (AI) services into your existing applications, unlocking en...

This comprehensive guide delves into the Saga pattern, a critical architectural approach for managing distributed transactions in microservices enviro...

The cloud architect plays a vital role in designing and implementing cloud solutions, a crucial function for modern business success. This guide explo...

This comprehensive guide provides a deep dive into implementing the Competing Consumers Pattern, a powerful architectural pattern for handling concurr...
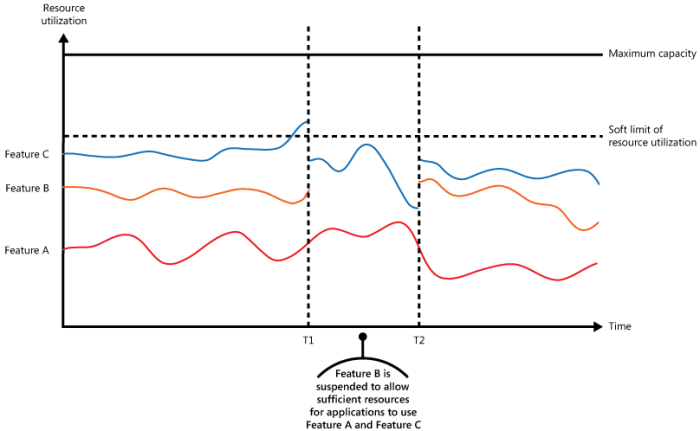
This comprehensive guide delves into the critical concept of throttling, exploring its mechanisms, patterns, and implementation strategies. From defin...
This article explores the dangers of premature optimization, a prevalent anti-pattern that can hinder software development progress. It outlines the c...

Discover the "Boy Scout Rule" in software development, a simple yet powerful principle for improving code quality and long-term project success. This...

Understanding Availability Zones (AZs) is crucial for building resilient cloud applications. This article provides a comprehensive overview of AZs, ex...
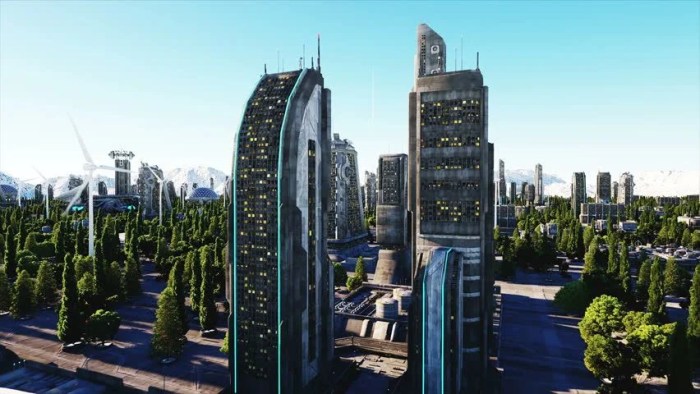
To thrive in today's dynamic digital environment, your cloud architecture needs to be ready for the future. This guide offers a comprehensive strategy...
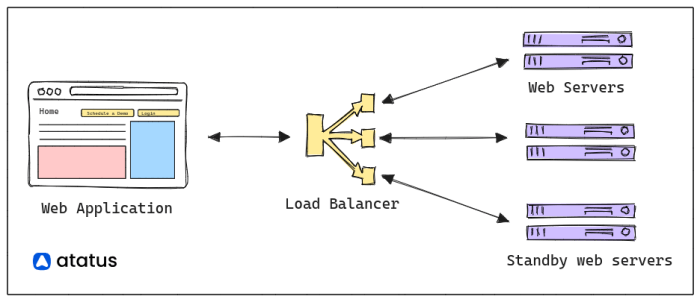
Modern distributed systems rely heavily on network communication, which inherently introduces challenges of unreliability. This article provides a cri...
This article explores the critical challenges inherent in microservices architectures, such as network latency, security vulnerabilities, and complex...